Global VoIP usage is soaring, with mobile VoIP users surpassing the one billion mark in 2017. But while there is significant growth, there’s also a genuine concern: security. According to IBM, over 50% of cybersecurity attacks target VoIP systems.
Cybercriminals are using increasingly sophisticated means and technologies to achieve their ends. A 2016 Verizon report showed that 70% of cyber-attacks use a combination of phishing and hacking to achieve success. Phishing scams are on the rise, and the rate at which they occur is set to increase.
Encryption services, then, have become an essential tool in the fight against online criminal behavior. Encryption ensures both personal and business assets remain secure and out of the hands of criminals.
As we move away from analog systems and ISDN towards Voice Over IP systems, we’re going to see big changes in the way we manage data security.
How does an IP phone work and why is it vulnerable? It uses the same infrastructure as your networks and internet traffic. As a result, it can be equally susceptible to the threats posed by cybercriminals to these systems. Traditional communications networks such as ISDN and POTS did not need the level of security and encryption that VoIP requires.
Cyber Security Needs For the Future
As ISDN becomes obsolete, encryption measures will be integral to the smooth operation of a healthy VoIP-based comms system.
British Telecoms stated they will begin phasing out ISDN networks as soon as 2020, and that they aim to transition to VoIP and dissolve ISDN fully by 2025.
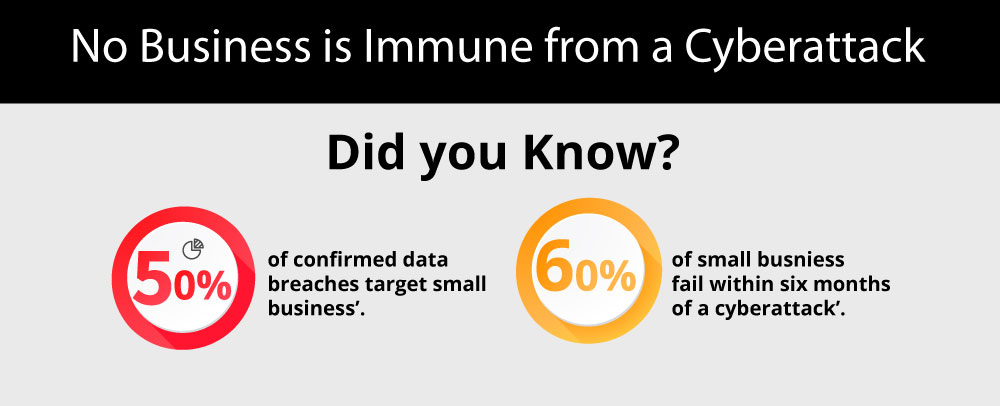
We will see significant changes in the landscape of communications networks and technology. As this happens we can expect to contend with a host of new security challenges. According to one analysis, cybercrime is set to cost businesses over $2 trillion by 2019.
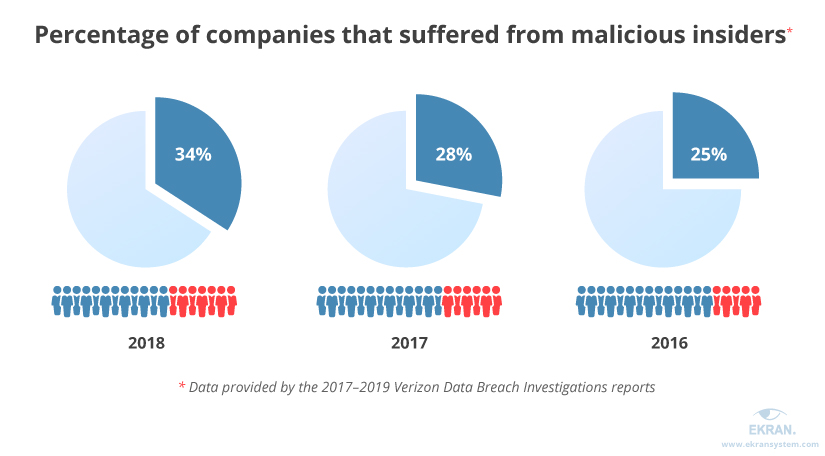
Source: Insider Threat Statistics for 2019: Facts and Figures | Ekran System
As we move to the next stage of communication and sales process revolution, it is of utmost importance that we maintain a high level of security. Companies will continue to pose the question on what are the benefits of applications for video calling. The answer is encryption. It will ensure that our sensitive data is unfathomable to those seeking to steal it for their benefit.
Criminals can hijack a call at any point along its communication journey. Data packets can be easily intercepted by your provider, and these data packets are vulnerable at any point of transit through the network.
Intercepting data is possible to people who either own the legal systems or by those that have successfully hacked them.
VoIP providers and cybersecurity experts have been working on solutions to ensure the privacy of high-value information.
VoIP comes with a range of encryption options and secure purpose-built software and networks. Users can rely on onion-style data protection and strict authorization protocols. It offers encrypted softphone tech that will help ensure your data integrity remains intact.
The amount of investment and R&D going into the encryption industry is significant. The result is advances in end-to-end encryption and Wi-Fi encryption. You can be sure to see some seismic shifts in the complexity of data protection measures in the future.
Most of the problems involved in communication security will be out of VoIP customers’ hands. But intelligent management of passwords and stored data can offer some level of protection and, as long as people follow correct security procedures and keep systems up to date, security should be tight.
VoIP providers similar to Mitel are working tirelessly to develop systems that cater to the needs of the consumer. Current predictions have VoIP users surpassing the 200 billion mark by 2020. Stats have shown VoIP was worth a staggering $77.4 billion as a market share value back in 2017.
All of this invested interest means you can expect even more security developments to ensure Voice Over IP remains a robust and viable industry.
Encryption security measures will act as part of a layered security system to protect your VoIP system. As James Scott, Cyber Security Advisor to Congress, stated:
“There’s no silver bullet solution with cyber security, a layered defense is the only viable defense.”
The diagram below gives insight into the current cyber security measures for: The New York Cybersecurity Requirements for Financial Services Companies.
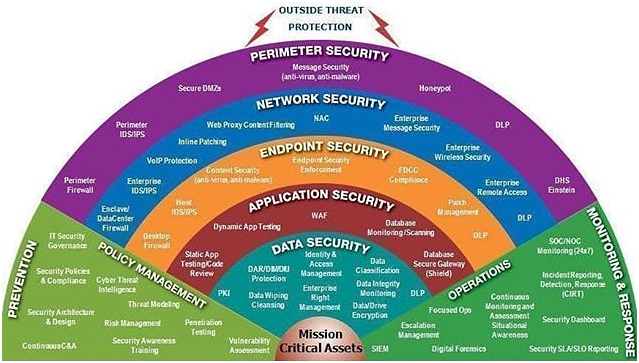
Source: New York Cybersecurity Requirements for Financial Services Companies (NYCRFSC)
Ensuring Your Security Is Relevant
As tech continues to evolve at breakneck speed, it can be challenging to keep up with every development. Encryption has been around for a very long time but its complexity has come a very long way.
As we speed into the future, we can do so with a certain amount of comfort in our ingenuity. We are masters of communication and group collaboration, and we are masters of encryption.
With breakthroughs happening all the time, we can be assured that encryption will be key to VoIP security. The recent groundbreaking record of 18-qubit entanglement by Xi-Lin Wang and his team of researchers at the University of Science and Technology of China, has been hailed as a significant leap forward.
We are one step closer to creating the next generation of computers capable of offering high-level encryption.
Watch this space as the two realms of VoIP and cyber security merge, making us more interconnected than ever before.
But with greater interconnectedness comes a more significant threat. We open ourselves up to being vulnerable on a global scale. People and businesses can operate anytime from anywhere in the world.
Our data can be intercepted easily and we need measures in place to prevent it happening. Cyber security is the key to making sure this doesn’t happen.
How private is your personal information? – YouTube
Encryption will be vital to keeping our information safe and secure to the organizational structure as VoIP rolls out across the globe. Savvy businesses and individuals already value the security that privacy brings. Encryption and VoIP are made for each other.
So let’s end with some wise words from IBM chief exec Ginni Rometty:
“We believe that data is the phenomenon of our time. It is the world’s new natural resource. It is the basis of competitive advantage, and it is transforming every profession and industry. If all of this is true – even inevitable – then cybercrime, by definition, is the greatest threat to every profession, every industry, every company in the world.”
