In early August, the popular customer management platform Twilio announced its employees were targeted with an SMS phishing scam, leading to unauthorized access to customer data. The cyberattack was carried out by sophisticated and coordinated threat actors and the investigation is still ongoing.
The company counts Lyft, Airbnb, Salesforce, Stripe, Zendesk, Uber, and Shopify as its high-profile customers. Apart from the bigwigs, a lot of Shopify and other ecommerce stores use Twilio to run omnichannel communications, social commerce, and platform security.
Twilio, despite boasting a highly secured infrastructure, couldn’t prevent the social engineering attacks. Unfortunately, this is not an anomaly. Many online and ecommerce businesses fail to meet customer data protection standards, leading to loss of revenue and worst of all, brand reputation.
According to a GreatHorn report, 65 percent of IT teams faced spear phishing attacks in 2021. If you’re running an online business, there’s a good chance your brand and customers might be targeted by cybercriminals. In this guide, I’ll go over the steps every online business should follow to stay on the safe side.
1. Ask yourself if you really need to collect this data
The first question you need to ask is this: “do we collect only the necessary data?” Diversifying data governance responsibilities and minimizing liabilities should be the first step for any online business today.
It’s easy to understand why most companies prefer to collect user data. In an age of market saturation, first-party data can help you understand buying triggers, selling challenges, and strategies that can push you ahead of competitors. More data you collect, the more accurate decisions you can make.
But having a huge repository of customer data also puts a target on your back. Hackers look to break into companies that host a large amount of sensitive data and if your servers are exposed in one of these attacks, the loss will be catastrophic.
To mitigate data theft in 2022 and retain customers, reconsider your data collection method. If a certain type of data is not directly attributable to internal services, allow a third-party to store them. This could be credit card and billing information or email addresses for marketing campaigns. By reducing the data coverage, you not only keep sensitive information in silos but also stay compliant vis-a-vis GDPR in case of cyberattacks. You should always have a contingency plan in place in case the data you collect does become leaked and you need to notify your customers and act to remedy the effects of the breach.
2. Make sure you use data encryption
When a customer shares personal information with you, they trust you to keep that data safe. The first thing you need to do is live up to their faith and encrypt all the sensitive data that might otherwise put a user at risk.
Data encryption is the method of converting plaintext into ciphertext. The encrypted ciphertext and decrypted plaintext can only be accessed with specific keys, which is the foundational concept of cryptography. Two of the most popular encryption methods are:
- Asymmetric encryption: It requires a public key to encrypt but a private key to decrypt data. Popular asymmetric encryption protocols such as RSA, DSS, and PKI are more secure because they don’t rely on sharing private keys, but the calculations often make them slow and inefficient.
- Symmetric encryption: It requires only one key to encrypt and decrypt data. Symmetric encryption compromises on security by relying on a single key to be shared between two parties but more than makes up for it in speed and efficiency. AES is the modern iteration of symmetric encryption that is both secure and efficient.
Any data that can be used to personally identify a user needs to be encrypted. Personally identifiable information (PII) includes login details, physical address, and other financial and health data. Exposed PII is often used for identity theft and once it’s stolen by hackers it is sold to the highest bidder on the dark web.
If you’re running an online business, you must protect the PII of users. If you’re not sure, ask your developers and run security audits to weed out flaws in your encryption mechanism.
3. Do you have SSL, and are you behind a firewall on your site?
PII encryption alone won’t help you protect your customers online—you must use SSL to encrypt the traffic as well. A secure socket layer (SSL) is an encryption protocol that encrypts the data between your servers and the user’s web browser. SSL and the modern TLS certificate authenticate the server to verify the user is indeed interacting with the correct party. These certificates prevent man-in-the-middle attackers from snooping into a conversation because all they’d get is encrypted gibberish.
A quick way to find if your web site has SSL/TLS enabled is by simply visiting the web site and checking the URL bar.
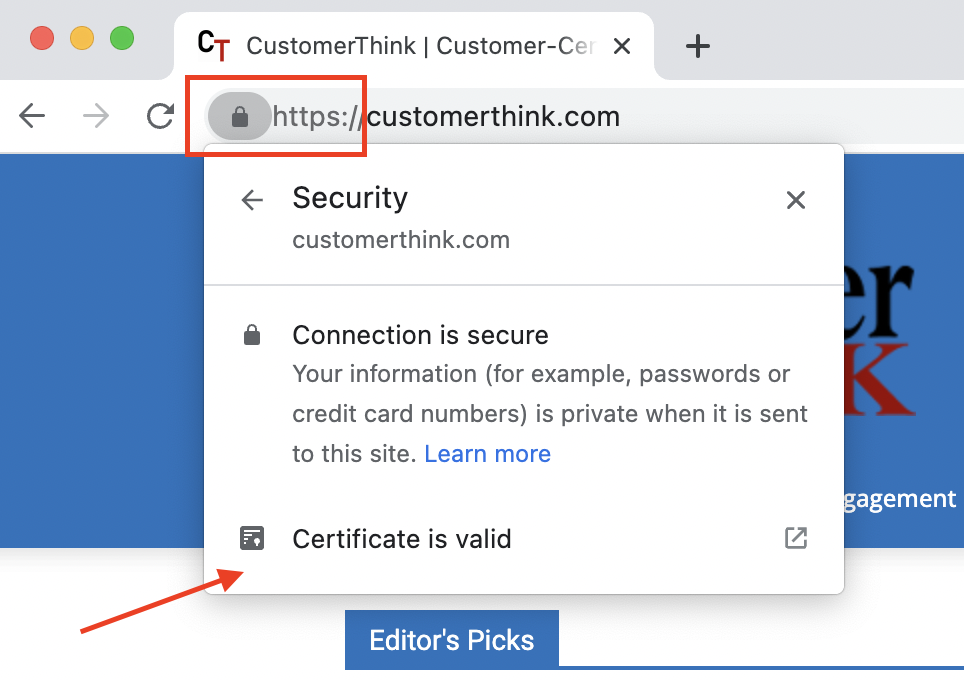
Does it look like the image above? If you find the HTTPS or the padlock icon in the URL bar, you’re encrypting the data between your servers and the users.
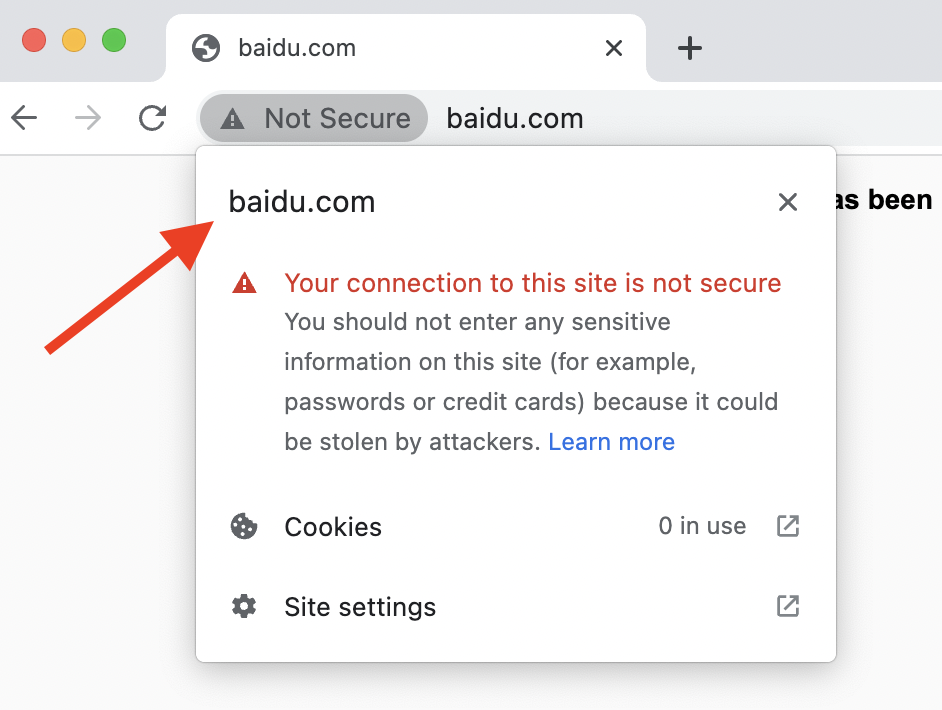
If your URL bar looks something like this one, then you have a problem.
SSL/TLS has become security due diligence in 2022 but it doesn’t hurt to check whether your web site certificate is valid occasionally. To obtain a valid certificate, apply for one from a trusted certificate authority and follow the verification process.
Apart from having a valid SSL/TLS certificate, you should also protect your public-facing web site from malicious intruders and hackers. A firewall protects your web site from unwanted traffic, SQL injection, cookie poisoning, and denial-of-service (DoS) attacks by allowing you to configure the IP parameters of visitors. It’s the first line of defense that monitors traffic, works as an antivirus, and shields web site assets from hackers. Since ecommerce web sites are targeted from various parts of the world, a firewall gives you a superior remote access control mechanism to fend off attacks.
4. Look into using mesh architecture for enhanced security
This is a bit of an advanced security step but might just put your online business up for success going forward. Gartner first introduced the term “cybersecurity mesh architecture” or (CASM) as one of the top technology trends for 2022 and it has caught the attention of security analysts and global businesses.
Mesh architecture plans to create a composable and interoperable architecture by recycling smaller parts and allowing various teams to contribute to building the organization’s information security. CASM is a macro concept that builds upon the micro trends of today, such as API-first technologies, zero-trust networks, and the need to break down security silos to allow experts to collaborate seamlessly. Since IoTs and collaborative ecosystems are central parts of CASM, Microsoft was one of the earliest companies to integrate mesh architecture in Microsoft Teams last year.
Since it’s cutting-edge technology, CASM will rely on the development of composable security tools and stronger data governance policies to make a mark. But on paper, it’s already showing results with Gartner predicting CASM will reduce 90 percent of the financial impact of cyberattacks.
5. Concluding tip: educate employees on security risks
If you can take one lesson away from the Twilio incident, it should be that no matter how strong your brand’s security measures are, the gatekeepers must be empowered to detect, address, and mitigate threats on their own.
Your employees need to be educated and constantly updated on the changing landscapes of data privacy, security, and compliance. You can start the process by shifting security to the left, which puts security at the heart of IT operations and privacy-first apps at the hands of employees and users. Here are five ways you can increase the level of awareness among the employees:
- Rework your cybersecurity jargon to make the concepts more consistent and accessible to everyone across the organization
- Regularly hold sessions and seminars with employees from all levels and explain the various impacts of cyberattacks
- Train and test the knowledge of employees by putting them in situations that mirror real-life hacking incidents
- Communicate upfront with employees in case of security breaches and allow them to submit queries and feedback on training programs. They must also feel comfortable sharing if they have been targeted by hackers.
- Put special emphasis on handling social engineering attacks. Rational knowledge and experience tend to fade away in front of cleverly executed phishing attacks that trigger emotional responses, so it’s important they’re able to mitigate risks as much as possible.
Part of shifting security to the left is allowing data privacy and security to be an ongoing part of company culture. When you blend technological measures with a redefined outlook toward security, you’re better equipped to protect your customer’s data.
