As we are quickly approaching the end of 2018, the prevalence and pervasiveness of data breaches are at an all-time high. As Wired reported earlier this year, “Corporate security isn’t getting better fast enough, critical infrastructure security hangs in the balance, and state-backed hackers from around the world are getting bolder and more sophisticated.”
October is cybersecurity awareness month, which means that now is the perfect time to reevaluate your company’s approach to insider threats and data loss prevention strategy.
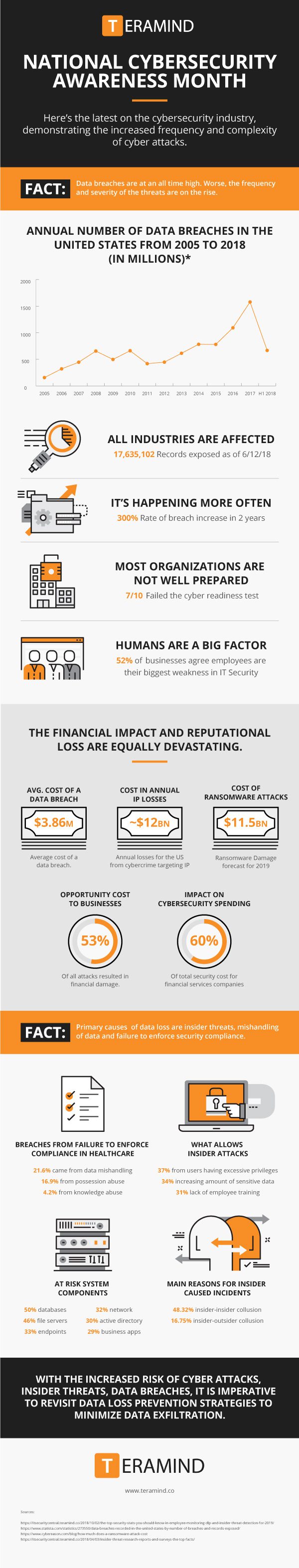
Data loss events are happening more frequently and at greater scale, costing companies money and damaging their brand reputation in the process. According to a 2018 study conducted by the Ponemon Institute, the average cost of a data breach rose by 6.4% in 2018 with most breaches costing a company $3.86 million. Unsurprisingly, mega breaches are becoming more costly for companies as well. The study estimates that data breaches involving one million records costs companies $40 million, and data breaches exceeding 50 million records cost $350 million.
The deluge of incredibly destructive, high profile data breaches has made cybersecurity a regular topic in boardrooms around the world. Even so, many organizations continue to use inferior products or are employing ineffective processes, especially when it comes to protecting against insider threats and data exfiltration.
While external threats gain a lot of publicity, one of the most prominent but overlooked hazards are companies’ own employees, ie the “insiders”. Whether they are intentionally malicious or accidentally sharing sensitive information, employees account for more data loss than high-stakes network hacks.
With the onslaught of new data privacy regulations – from Europe’s GDPR legislation to California’s 2020 benchmark for stringent privacy laws – there is no time like the present to fortify your company’s approach to data loss prevention to ensure that you are prepared for 2019 and beyond.
When evaluating your data security strategy, there are some essential elements to prioritize.
Consider User Behavior As Part of Your Data Security Strategy
Typically, insider threats can be identified by users’ abnormal digital behavior. For instance, a rogue employee may begin accessing company data at odd times or from different locations; or an employee may spend time on job search sites while downloading company’s CRM records.
Therefore, transition away from systems that exclusively rely on access logs and access level protection to complete a threat analysis. Instead, complement these protocols with activity monitoring to create a complete picture of possible vulnerabilities while providing IT administrators the ability to evaluate and respond to threats in real time.
Deploy Tools that Leverage Machine Learning to Detect Anomalies
Fortunately, activity monitoring has progressed significantly since it was first introduced, and its capabilities are bolstered by advancements in machine learning. Consequently, companies should deploy a security solution that leverages machine-learning to identify anomalies.
Even the most comprehensive acceptable use policies are difficult to monitor, but modern security systems that apply machine learning to use clustering and analytics can create a baseline of user behavior so that they can detect actions that deviate from the norm.
For best results, pursue solutions that combine user behavior analytics with rules-based DLP.
Deploy a Comprehensive System With a Common Sense Approach
Ultimately, companies benefit most when they implement a comprehensive system for protecting their data with a common-sense human-centric approach. Companies put themselves in a position to succeed when they:
1. Monitor specific elements of user behavior that make sense within the parameters of the company and how users access information.
2. Utilize recording applications for training opportunities or forensic purposes. Full forensic capabilities including a live video recording of user activity and reliable records of employee access provide a glimpse into the past to help determine the needs of the future.
3. Leverage a behavior-centric approach within the framework of a sensibly defined and customizable use policy for employees and third-party contacts.
The threats to data security are not diminishing, but there are leadership techniques and technological tools available to help fight this reality. Cybersecurity month is an opportunity to remember the importance of a comprehensive data security plan. It’s time to take your organization’s defensive posture to the next level.
This article was originally published on IT Security Central and was reprinted with permission.



