Digital security is no longer just the chief technology officer’s concern. Protecting identities and data falls on every person working for a company, but it should begin in the C-Suite. As the owner or CEO, it is your duty to keep abreast with the current and forthcoming technologies to help your business evolve. Studies show that customers trust businesses that are able to secure their privacy and confidential information.
You know it is time to level up your game. Start with these 5 authentication models that are reshaping the security and protection landscape:
Single Sign-On
Replacing the traditional password method, single sign-on or SSO provides a more streamlined solution to users with multiple passwords. Instead of maintaining a set of login credentials for each account you keep, you only need a master password to access everything in one go. Integrated into a multi-factor authentication system, it is also one of the safest and most secure baselines to date.
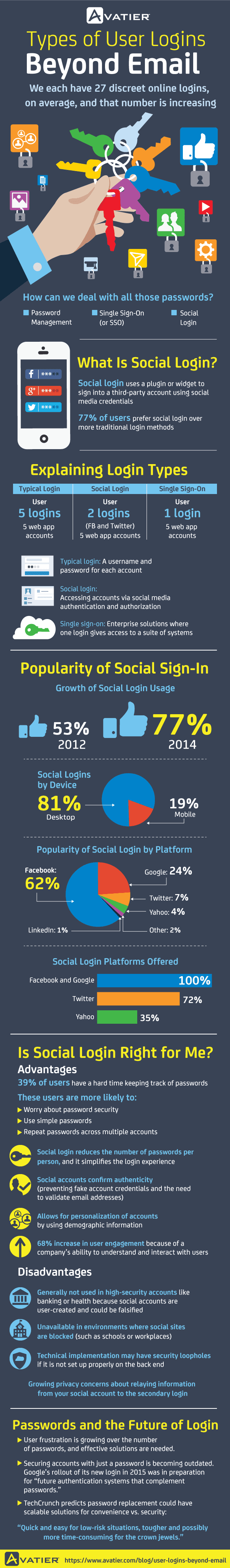
Social sign-in is the most preferred SSO, with 77% of consumers on board, according to Avatier. Facebook and Google come out on top, with 62% and 24% users, respectively. Twitter follows at 7%, then Yahoo (4%), other platforms (2%), and LinkedIn (1%). See the infographic below to learn more about how social sign-in works:
Adaptive Authentication
When partnered with baseline login solutions such as SSO, adaptive authentication is a force to reckon with. Instead of unique fingerprints or voice prints, it analyzes behavioral patterns. Up to this point, the tech can detect changes such as hesitance in typing a password or the movement of the mouse. If it recognizes differences, it will force the user to go through more authentication steps and send an alert to the tech team.
Adaptive authentication bears a lot of promise. But like other biometric authentication models, it is also high risk. It can be subjected to abuse especially by determined hackers and during covert operations, in which behavioral patterns can be observed and copied.
Speaker verification
Speaker authentication is classified as a behavioral biometric. It determines learned behavioral patterns such as voice pitch and speaking style. For instance, a person may claim that he or she is the owner of a certain phone. This method will verify the claim based on a voice print that was registered as that of the owner. It will take some effort to teach customers how to enroll their voice print. But the system is pretty easy to roll out.There are no additional hardware costs needed. Dedicated programs can use existing microphones in smartphones.
Fingerprint authentication
Each human has a unique set of fingerprints. This fact has made it possible to verify that a person is who he or she claims to be. Using fingerprint sensors, fingerprints are captured through a live scan and digitally processed to create a biometrics template. This template is stored to facilitate matching.
Fingerprint recognition is pretty common in smartphones these days. Apple, Samsung, Motorola, and Oppo have introduced the tech in recent models. But Motorola was the pioneer in 2011. There are no reasons to oppose the idea that scanners will become more sophisticated in the near future.
Iris scan
Often called a retina scan, albeit mistakenly, an iris scan uses mathematical patterns to recognize an individual. Like fingerprints and voice prints — yeah, you guessed it right — our irises have complex and unique patterns. An iris scan is speedy when matching. It is also said to be 10 times more accurate and reliable than a fingerprint scan. Like voice, there is no need for a physical contact, though you cannot use it remotely.
It is not yet common as a security and privacy tool for people. Instead, iris scans have been mainly used in immigration lines to facilitate a faster passport or national ID authentication process.
Explore other CustomerThink articles for more information on how you can improve digital security through biometric authentication for your customers.



![[Research Round-Up] New Study Shows the Continuing Value of B2B Thought Leadership](https://customerthink.com/wp-content/uploads/development-2010010_1280-pixabay-innovation-ideas-think-1-218x150.jpg)